Strange strings appear across the internet every day. Some show up in software logs. Others appear in code repositories, error reports, or debugging outputs. One example that has recently caught attention is 73deb40.
At first glance, it looks cryptic. It does not resemble a word, number, or recognizable identifier. Naturally, people search what is 73deb40 hoping to uncover hidden meaning.
The truth is less mysterious but far more interesting.
73deb40 is typically a shortened hexadecimal hash identifier used in computing systems, particularly in version control tools like Git, log tracking systems, and software builds. While it may look random, it usually represents a specific reference to data, code changes, or system events.
Understanding how identifiers like 73deb40 work reveals something deeper about modern software architecture. Today’s digital infrastructure relies heavily on hashes, unique identifiers, and traceable reference codes to manage massive volumes of data.
This article explains:
- What 73deb40 actually means
- Why hexadecimal identifiers are used in computing
- Where you might encounter this code
- How hashing systems generate identifiers
- Whether 73deb40 is related to security risks or malware
- Why developers rely on short hashes in modern systems
By the end, the mystery behind 73deb40 will disappear—and you will gain insight into how modern software systems track and organize information.
Quick Definition of 73deb40
The Simple Explanation
The identifier 73deb40 is most commonly a short hexadecimal hash. In many cases, it functions as a Git commit reference.
When developers modify code in a repository, version control systems assign each change a unique hash value. The full hash may be long—often 40 characters in systems that use SHA-1 hashing.
To make the identifier easier to read and reference, developers frequently use a shortened version. That shortened value can look like 73deb40.
In simple terms, this identifier acts as a reference point. It allows developers to:
- Locate a specific code change
- Identify a particular software version
- Trace debugging information in logs
- Track deployments in software pipelines
Even though the string appears random, it represents a specific technical state within a system.
Why It Looks Confusing to Non-Developers
For someone unfamiliar with software systems, 73deb40 can look suspicious.
There are several reasons for this:
- It contains letters and numbers with no obvious meaning
- It appears without context in logs or tools
- It resembles encryption or hidden codes
- Many users associate unknown strings with malware
However, most short hash identifiers are completely normal. They are simply machine-friendly labels used to track data and events.
Understanding the Structure of 73deb40
To understand why identifiers like 73deb40 exist, we first need to explore the numbering system behind them.
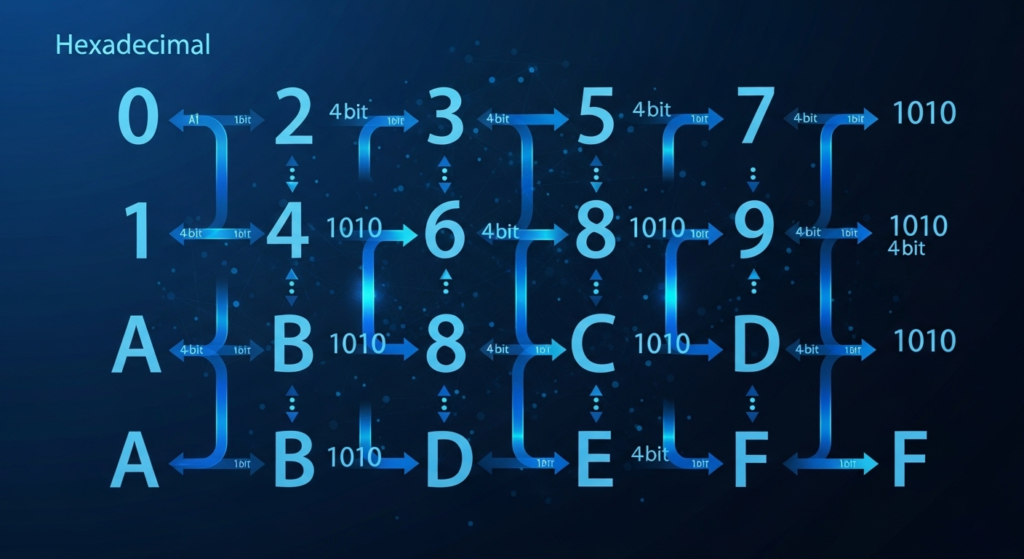
The Hexadecimal Number System (Base-16)
Computers ultimately operate using binary numbers. Binary uses only two digits:
- 0
- 1
However, long binary sequences are difficult for humans to read. Engineers often convert binary into hexadecimal format, which uses base-16 numbering.
Hexadecimal uses the following characters:
| Decimal | Hexadecimal |
|---|---|
| 0–9 | 0–9 |
| 10 | A |
| 11 | B |
| 12 | C |
| 13 | D |
| 14 | E |
| 15 | F |
This means hexadecimal can represent large binary values in a compact and readable format.
For example:
| Binary | Hexadecimal |
|---|---|
| 1110 | E |
| 1011 | B |
| 0100 | 4 |
This relationship explains why identifiers like 73deb40 contain both letters and numbers.
Relationship Between Hexadecimal and Binary
Each hexadecimal digit represents four binary bits.
That makes hexadecimal extremely useful for:
- Memory addresses
- Machine instructions
- Hash values
- Debugging outputs
Engineers often prefer hexadecimal because it compresses binary into manageable segments.
Without hexadecimal notation, system identifiers could become extremely long and difficult to interpret.
Why the Identifier Contains Seven Characters
Git and similar systems often shorten hashes to the first seven characters.
Why seven?
Because in most repositories, seven characters provide enough uniqueness to identify a commit.
The full hash might look like this:
But developers usually reference the commit using the shorter version:
This approach improves readability while maintaining reliable identification.
Where 73deb40 Comes From Behind the Scenes
Hashing Algorithms Used in Software Development
Hashes are generated by hashing algorithms, mathematical functions that convert data into fixed-length values.
One algorithm historically used in Git is SHA-1, which produces a 40-character hash.
Key characteristics of hashing algorithms include:
- Deterministic output
- Fixed-length results
- High uniqueness
- One-way transformation
That means the same input always produces the same hash value.
How a Full Hash Becomes 73deb40
Below is a simplified explanation of how the identifier might appear.
| Step | Process | Result |
|---|---|---|
| 1 | Developer commits code changes | Repository updated |
| 2 | Git applies hashing algorithm | Full SHA hash generated |
| 3 | System displays shortened version | 73deb40 |
| 4 | Hash appears in logs and builds | Commit reference |
This shortened hash allows developers to quickly reference specific code changes.
Why Systems Shorten Hashes
Short hashes provide several advantages:
- Easier for humans to read
- Faster to type in command-line tools
- Simpler debugging references
- Cleaner log output
Despite being shortened, they remain accurate identifiers within a repository context.
Real Systems Where You Might Encounter 73deb40
Many people first encounter identifiers like 73deb40 while investigating technical logs or repositories.
Here are common places where these identifiers appear.
Version Control Systems
Version control systems track changes in software projects.
Popular systems include:
- Git
- Mercurial
- Subversion
In Git, each commit generates a unique hash identifier.
Developers often reference commits using short hashes like 73deb40 when they:
- review code history
- revert a change
- inspect a specific update

Server Logs and Debugging Tools
System logs often contain identifiers that help engineers trace issues.
For example:
- deployment identifiers
- request tracing codes
- error references
- crash markers
A string like 73deb40 might appear in logs to identify the exact software version running when an error occurred.
This dramatically improves debugging efficiency.
Databases and Backend Infrastructure
Backend systems frequently use identifiers for:
- data objects
- transactions
- execution traces
- query monitoring
In large-scale applications, thousands of events occur every second. Without identifiers, tracking system behavior would be impossible.
APIs and Microservices
Modern software architecture often relies on microservices.
Each service communicates with others through APIs. To track requests across systems, engineers attach identifiers to each transaction.
These identifiers help with:
- tracing request paths
- diagnosing performance issues
- monitoring system health
Short codes similar to 73deb40 can appear in API logs or debugging dashboards.
Cloud Platforms and DevOps Pipelines
Continuous integration and deployment pipelines also generate identifiers.
These might represent:
- build versions
- container image hashes
- deployment references
DevOps teams rely on these identifiers to determine exactly which code version is running in production.
Why Modern Systems Use Identifiers Like 73deb40
As software systems scale, tracking information becomes increasingly complex.
Short identifiers solve several critical problems.
Scalability in Distributed Systems
Modern platforms may process millions—or even billions—of events daily.
Without identifiers, systems could not reliably track:
- code changes
- transactions
- system events
Short hashes provide a lightweight method for referencing complex data structures.
Data Traceability
Traceability is essential in modern software systems.
Developers often need to reconstruct events that caused failures.
For example:
- Which commit introduced a bug?
- Which build deployed a faulty version?
- Which service triggered a crash?
Identifiers like 73deb40 allow engineers to answer those questions quickly.
Efficiency Compared to Sequential IDs
Different systems use different identifier formats.
| Identifier Type | Typical Length | Primary Use | Collision Risk |
|---|---|---|---|
| Short hash | 7 characters | Commit tracking | Low |
| UUID | 36 characters | Global identifiers | Very low |
| Sequential ID | Variable | Database rows | Moderate |
| Full SHA hash | 40+ characters | Cryptographic identity | Extremely low |
Short hashes strike a balance between readability and uniqueness.
Is 73deb40 Random or Algorithmically Generated?
Many people assume identifiers like 73deb40 are random.
They are not.
Deterministic Nature of Hashing
Hash functions are deterministic.
This means:
- The same input always produces the same output.
- Different inputs almost always produce different outputs.
For example, a code change combined with repository metadata produces a unique hash value.
Why It Appears Random
Hash algorithms are designed to produce outputs that look random.
This property prevents patterns from emerging and improves collision resistance.
Even tiny changes in input produce drastically different outputs.
This phenomenon is known as the avalanche effect.
Why Collisions Are Rare
A collision occurs when two different inputs produce the same hash.
Good hashing algorithms minimize this risk.
For example:
- SHA-1 produces over 1.4 trillion trillion trillion trillion possible values.
Although theoretical collisions exist, they remain extremely rare in everyday development workflows.
Is 73deb40 a Security Risk or Malware Code?
Because mysterious strings often appear in cybersecurity reports, users sometimes worry that 73deb40 indicates malware.
In most cases, that assumption is incorrect.
Common Misconceptions
Some online discussions claim that codes like 73deb40 represent:
- hidden cryptocurrency transactions
- hacker identifiers
- secret encryption keys
These interpretations are usually incorrect.
Without context, the string is simply an identifier.
How Malware Hashes Actually Work
Cybersecurity systems use hashes to identify malicious files.
Security tools often rely on SHA-256 hashes, which are much longer.
These hashes uniquely represent file contents.
Threat intelligence databases compare hashes to detect malware signatures.
A short identifier like 73deb40 alone rarely indicates a security threat.
When a Hash Could Be Security Related
Identifiers become relevant in cybersecurity only when:
- they match known malware signatures
- they appear in security alerts
- they are associated with suspicious processes
Even then, analysts typically rely on full hash values, not shortened fragments.
73deb40 vs Other Identifier Formats
Different systems use different identifier types.
Understanding the differences helps clarify the role of short hashes.
Short Hash vs UUID
UUIDs are longer identifiers designed for global uniqueness.
Example format:UUIDs are useful for distributed databases, while short hashes work well for repository tracking.
Hash vs Token vs Session ID
Identifiers serve different purposes:
| Identifier | Purpose |
|---|---|
| Hash | Identifies data or code changes |
| Token | Grants temporary access |
| Session ID | Tracks user sessions |
Short hashes like 73deb40 are typically data references, not authentication tokens.
When Developers Choose Each Identifier
Developers select identifiers based on system requirements:
- Hashes for data verification
- UUIDs for global uniqueness
- Sequential IDs for simple databases
- Tokens for authentication
Choosing the right identifier type improves system reliability.
Why People Keep Searching What Is 73deb40
Search trends often reveal how people interact with technology.
Several factors explain why this identifier attracts attention.
Encountering Codes in Logs
Developers and administrators frequently encounter unknown strings when investigating system logs.
When an unfamiliar code appears repeatedly, curiosity naturally leads to search engines.
Curiosity From Unusual Strings
Rare alphanumeric combinations often gain attention because they:
- look mysterious
- appear technical
- lack clear explanations online
Once search engines index such strings, more users begin searching them.
Confusion Caused by Technical Output
Software tools sometimes display identifiers without explanation.
Non-technical users encountering these values may assume something unusual is happening.
In reality, they are simply internal system references.
How Developers Use Short Hashes for Debugging
Short hashes are extremely valuable during debugging.
Tracking Code Changes Quickly
Developers can run commands that display commit history.
Using short hashes, they can quickly identify:
- which change introduced a bug
- which version is currently deployed
- which developer committed a change
Reproducing Bugs
Reproducing issues often requires running the exact code version where the problem occurred.
A hash identifier ensures the correct commit is located.
Coordinating Development Teams
Large development teams rely on hashes when discussing code.
A typical conversation might include statements like:
“The issue started after commit 73deb40.”
This simple identifier immediately tells the team which code snapshot to investigate.
Can 73deb40 Be Decoded?
Many people wonder if identifiers like 73deb40 can be decoded to reveal original data.
The answer is no.
One-Way Hash Functions
Hashing algorithms are designed to be one-way functions.
That means:
- data can be converted into a hash
- the original data cannot be reconstructed from the hash
This property makes hashes useful for both data integrity and security.
What the Hash Actually Represents
Although it cannot be decoded, the hash corresponds to a specific dataset.
In Git, that dataset may include:
- file contents
- commit messages
- timestamps
- parent commit references
The hash acts as a fingerprint of that information.
Should Regular Users Care About 73deb40?
For most people, identifiers like 73deb40 are simply background infrastructure.
For Developers
Developers rely heavily on hash identifiers for:
- version tracking
- debugging
- deployment monitoring
- code collaboration
Without them, managing modern software projects would be far more difficult.
For Everyday Users
Most users will only encounter such identifiers when:
- reading technical logs
- reporting software bugs
- exploring developer tools
In those contexts, the identifier itself is usually harmless.
When Investigation Is Necessary
Investigation may be necessary if identifiers appear alongside:
- security warnings
- application crashes
- suspicious system activity
Even then, the identifier alone does not indicate a threat.
Key Takeaways About 73deb40
Here are the most important points to remember:
- 73deb40 is typically a shortened hexadecimal hash identifier
- It often appears in Git repositories, server logs, and software builds
- The identifier originates from hashing algorithms
- Short hashes help developers track code changes efficiently
- They play an important role in debugging, monitoring, and infrastructure management
- In most cases, 73deb40 is not related to malware or security threats
Understanding identifiers like this improves overall technical literacy.
Frequently Asked Questions
What exactly is 73deb40?
It is typically a short hexadecimal hash identifier used in software systems, especially as a shortened Git commit reference.
Why do systems use identifiers like 73deb40?
Short identifiers help developers track code versions, debug systems, and manage large infrastructures efficiently.
Where might I encounter 73deb40?
You may see it in:
- code repositories
- server logs
- debugging tools
- deployment pipelines
- API request traces
Can 73deb40 be converted into readable text?
No. Hash identifiers are generated using one-way algorithms, which means they cannot be reversed.
Is 73deb40 dangerous?
No. In most situations it is simply a technical reference used within software systems.
Final Thoughts
The mysterious appearance of 73deb40 becomes much clearer when viewed through the lens of modern software engineering.
Behind the string lies an entire ecosystem of hashing algorithms, version control systems, and distributed infrastructure.
Short hexadecimal identifiers help developers track millions of events, changes, and deployments across complex systems.
While the code itself may look cryptic, its purpose is straightforward: providing a precise reference to a specific piece of data or code.
Understanding identifiers like 73deb40 offers a small glimpse into the invisible machinery that powers today’s digital world.